Analyzing Router Logs in Network Forensic Investigation | Infosavvy Security and IT Management Training
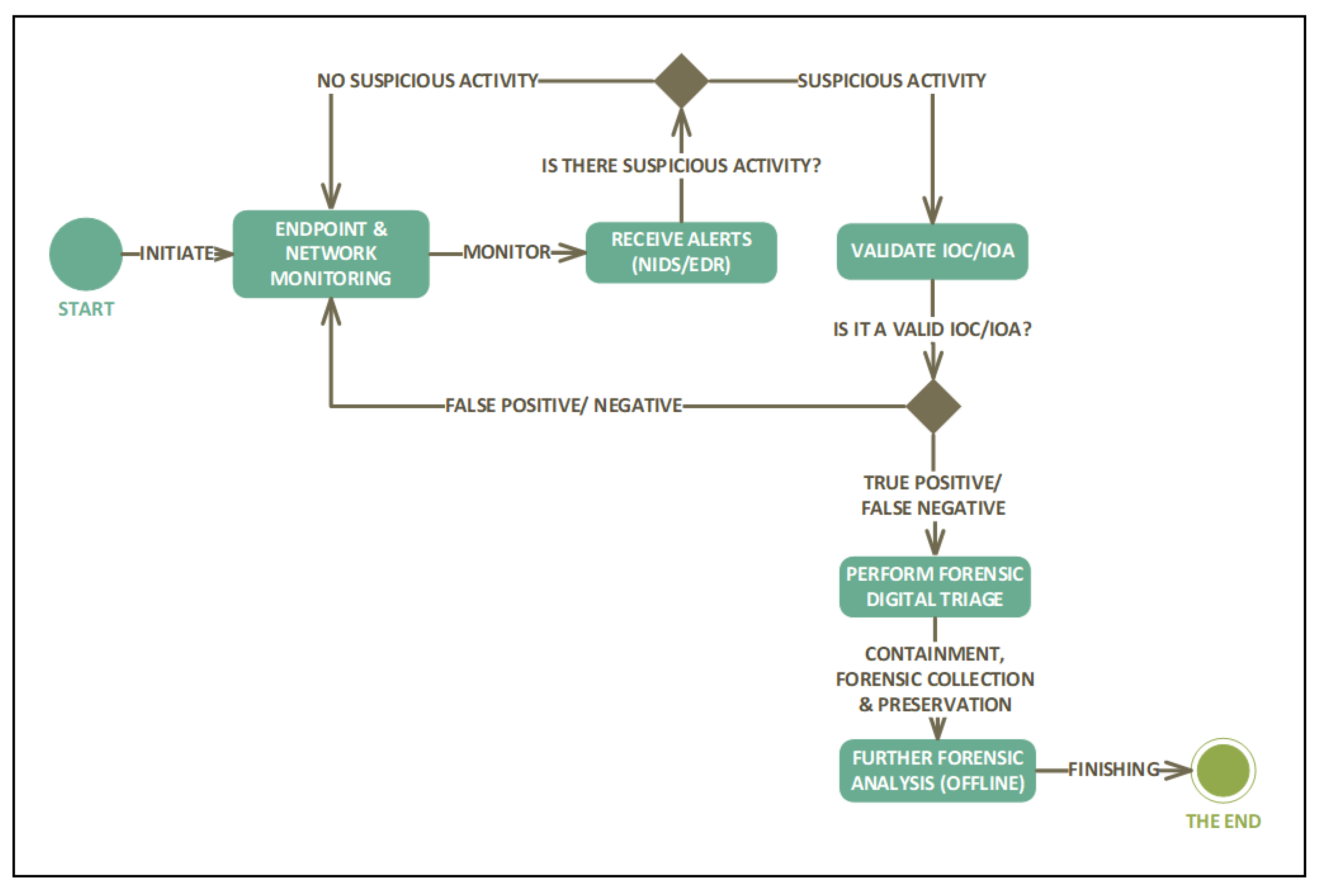
Applied Sciences | Free Full-Text | Investigating Proactive Digital Forensics Leveraging Adversary Emulation

Cisco Router and Switch Forensics: Investigating and Analyzing Malicious Network Activity 1st, Liu, Dale, Dale Liu, eBook - Amazon.com
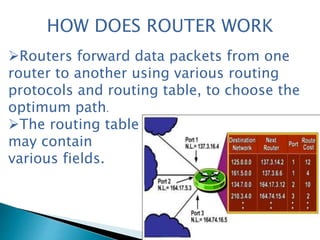
Forensics Book 4: Investigating Network Intrusions and Cybercrime Chapter 4: Router Forensics. - ppt download
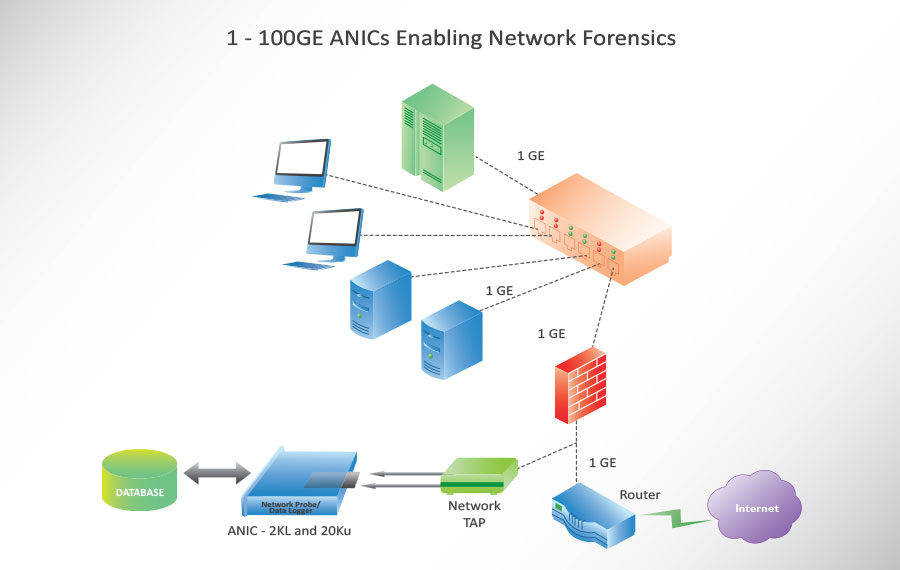
Network Security, Cyber Security & Forensics | Accolade Technology - Intelligent Host CPU Offload 1-100GE

Cisco Router and Switch Forensics: Investigating and Analyzing Malicious Network Activity: Dale Liu: 9781420064834: Amazon.com: Books