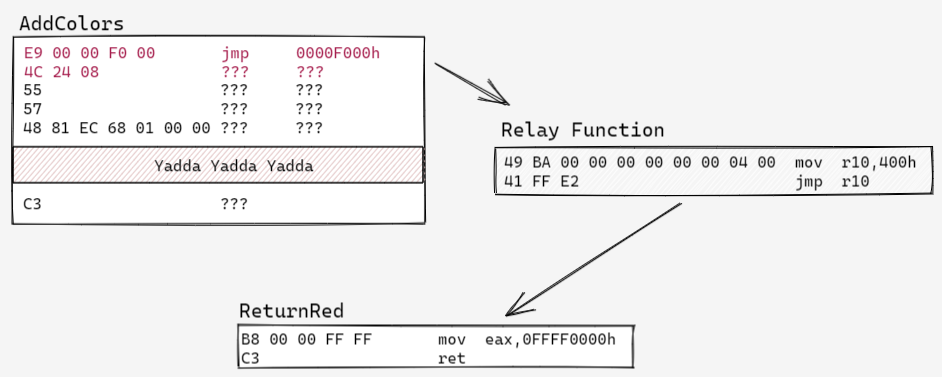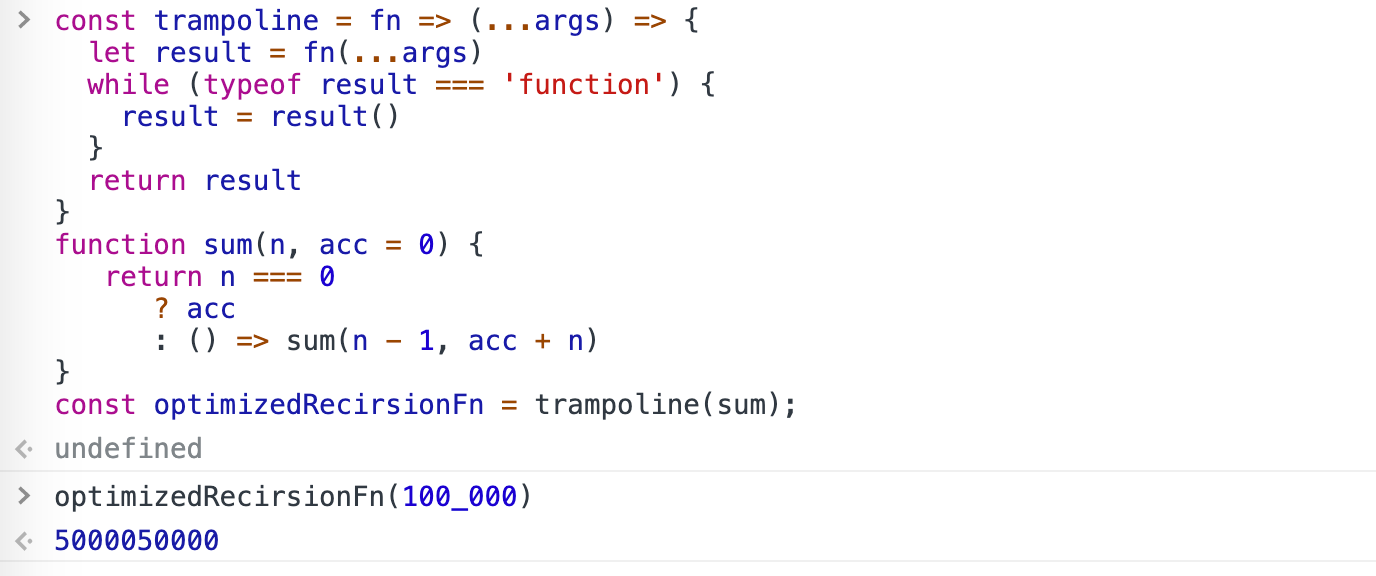
JavaScript: Recursion, Tail-Call Optimization and Trampolining with Pictures | by Vladimir Topolev | JavaScript in Plain English

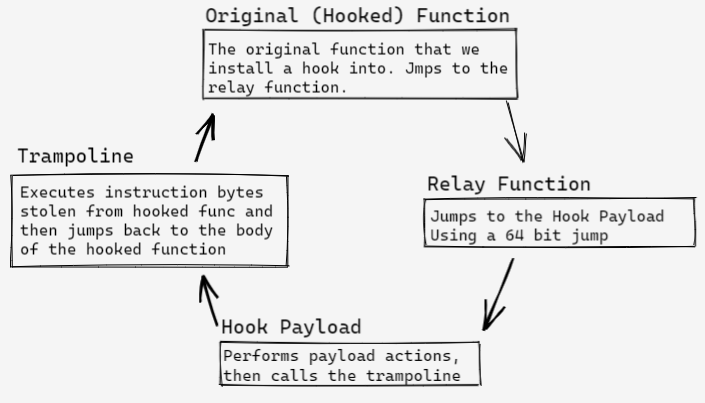
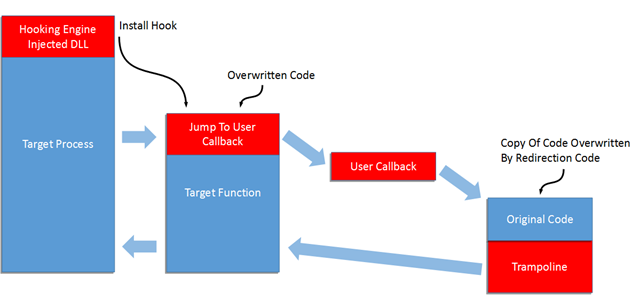
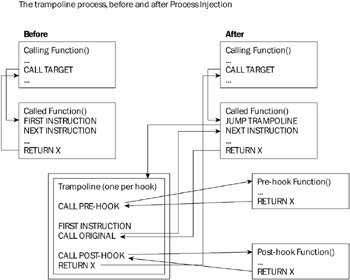
Trampoline Structure (Non-threaded Version of Paradyn) The entry point... | Download Scientific Diagram

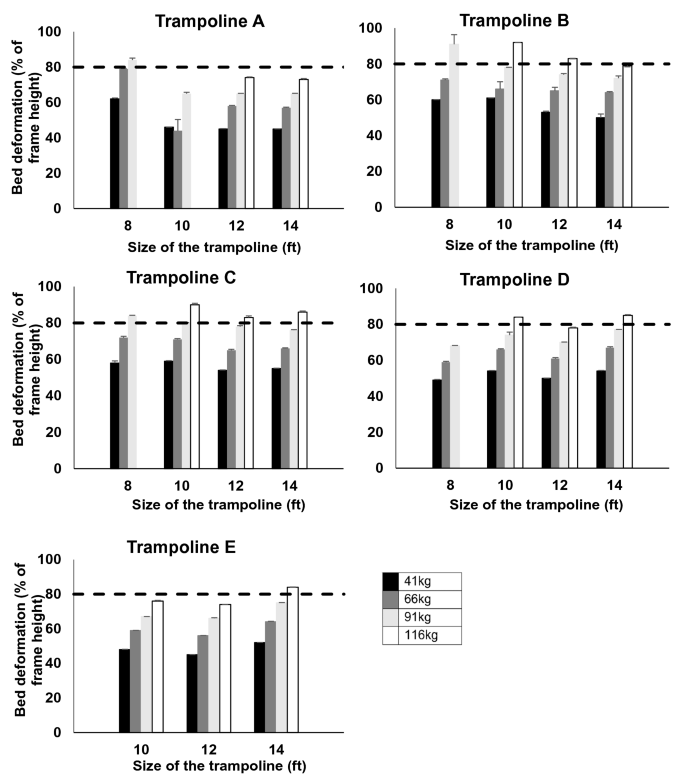
12FT Outdoor Big Trampoline,Outdoor Trampoline with Inner Safety Enclosure Net,Ladder,PVC Spring Cover Padding,Recreational Trampolines Fitness Trampoline for Kids,Black & Orange Color - Walmart.com